filewalld官网
firewalld是对iptables的封装,使防火墙管理起来更容易更清晰, 本质上是 firewald操作iptables操作netfilter, 底层始终是netfilterfirewalld使用zone(区域)概念,相当于Windows的专用网络公用网络等, 其实质是一套套规则, 方便切换firewalld的每个zone指定了target, 就是iptables的targetfirewalld的zone指定了端口port,和服务serviceCentOS7的firewalld默认是启用的
使用systemctl命令时, firewalld等效firewalld.service
### 启用firewalld服务, 开机启动firewalld服务
sudo systemctl enable firewalld
sudo systemctl enable firewalld.service
### 查看是否已启用firewalld服务,是enable启用还是disable禁用? 有可能启用但未启动,也可能禁用但当前启动
systemctl is-enabled firewalld.service
### 禁用firewalld服务, 系统启动时不开启firewalld服务
sudo systemctl disable firewalld
sudo systemctl disable firewalld.service
### 查看firewalld服务是enable启用还是disable禁用? 有可能启用但未启动,也可能禁用但当前启动
systemctl is-enabled firewalld.service
### 启动firewalld服务
sudo systemctl start firewalld
sudo systemctl start firewalld.service
### 停止firewalld服务
sudo systemctl stop firewalld
sudo systemctl stop firewalld.service
## 使配置或修改立即生效
### 重启firewalld服务, 会断开已有连接, 可以在服务停止状态执行
sudo systemctl restart firewalld
sudo systemctl restart firewalld.service
### 重新加载firewalld, 不会断开已有连接, 不能在firewalld服务处于停止状态的时候执行
sudo firewall-cmd --reload
比如: 远程控制台已建立连接, 此时本地关闭22端口,–delete-service ssh服务,
执行firewall-cmd --reload并不会断开连接, 但远程退出后就无法登录了执行 systemctl restart firewalld 则远程连接立即断开sudo systemctl status firewalld
sudo systemctl status firewalld.service
sudo firewall-cmd --state
查看已启用的服务列表;systemctl list-unit-files|grep enabled
查看启动失败的服务;systemctl --failed
cd /usr/lib/firewalld/
ls /usr/lib/firewalld/
cd /etc/firewalld
ls /etc/firewalld
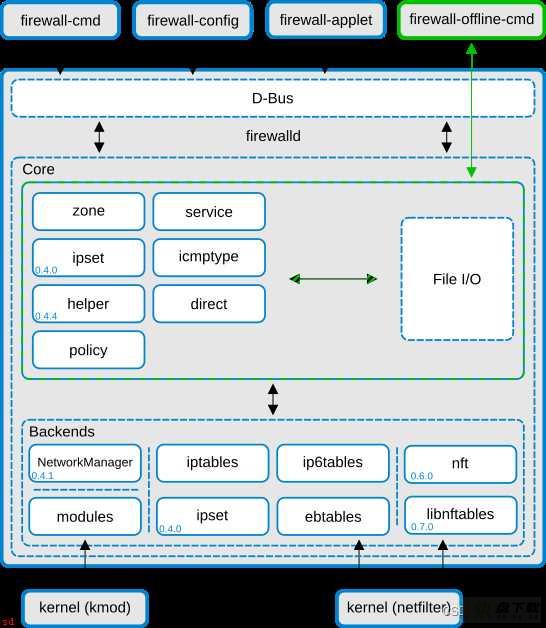
控制台操作 firewalld , 用 firewall-cmd 或 firewall-offline-cmd命令, 而不是 firewalld
offline是脱机的,离线的意思.
两种开头大部分用法相同, 但也有一些区别,比如
运行时可以使用firewall-cmd --reload 命令, 但没有 firewall-offline-cmd --reload 命令firewall-offline-cmd 可以在非运行状态执行, 很多命令本身就是永久生效的,用man firewall-cmd和man firewall-offline-cmd可查看说明手册
用firewall-cmd --help 和 firewall-offline-cmd --help 可以查看帮助
firewall-cmd --help | grep port 查看port相关的帮助内容
firewall-cmd --help | grep service 查看service相关的帮助内容
firewall-cmd --help | grep zone 查看zone相关的帮助内容
firewall-cmd --help | grep interface 查看interface相关的帮助内容
permanent
firewall-cmd命令语句中的一些设置, 加--permanent 才永久生效,
不加--permanent的话
有些设置本身就永久生效, 不用加,也不能加--permanent
firewall-offline-cmd开头的命令,一般都不能加--permanent , 本身就是永久的
firewalld官方文档—Zone
firewalld的zones类似Windonws的专用网络公用网络等, 相当于规则模板, 有利于管理的方便
firewalld使用zone(区域)概念,相当于Windows的专用网络公用网络等, 其实质是一套套规则, 方便切换firewalld的每个zone指定了target, 就是iptables的targetfirewalld的zone指定了端口port,和服务service来自官方文档 https://firewalld.org/documentation/zone/predefined-zones.html
Predefined Zones 预定义区域
drop 信任度最低
These are the zones provided by firewalld sorted according to the default trust level of the zones from untrusted to trusted:
下面这些是 firewalld 提供的预定义区域;根据其默认的信任级别从不信任到信任排序, 按信任度从低到高排列blockAny incoming network packets are dropped, there is no reply. Only outgoing network connections are possible.
任何传入的网络数据包都被丢弃;没有回复。 只有传出网络连接是可能的。 只能发送,不能接收publicAny incoming network connections are rejected with an icmp-host-prohibited message for IPv4 and icmp6-adm-prohibited for IPv6. Only network connections initiated within this system are possible.
任何传入的网络连接都会被拒绝;并使用 IPv4 的 icmp-host-prohibited 消息和 IPv6 的 icmp6-adm-prohibited 消息。 只有在该系统内发起的网络连接是可能的。
被拒绝的连接会收到一个icmp;返回目标主机不可达。externalFor use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.
用于公共区域。 您不相信网络上的其他计算机不会损害您的计算机。 仅接受选定的传入连接。
这也是firewalld默认的区域,默认不开放22以外的任何端口,需手动添加dmzFor use on external networks with masquerading enabled especially for routers. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.
用于启用伪装的外部网络;尤其适用于路由器。 您不相信网络上的其他计算机不会损害您的计算机。 仅接受选定的传入连接。workFor computers in your demilitarized zone that are publicly-accessible with limited access to your internal network. Only selected incoming connections are accepted.
对于您的非军事区内的计算机可以公开访问;但对您的内部网络的访问权限有限。 仅接受选定的传入连接。homeFor use in work areas. You mostly trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.
internalFor use in home areas. You mostly trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.
用于工作区域。 您主要相信网络上的其他计算机不会损害您的计算机。 仅接受选定的传入连接。trusted 信任度最高For use on internal networks. You mostly trust the other computers on the networks to not harm your computer. Only selected incoming connections are accepted.
用于内部网络。 您主要相信网络上的其他计算机不会损害您的计算机。 仅接受选定的传入连接。All network connections are accepted.
接受所有网络连接。相当于关闭防火墙
firewalld可以指定一个default zone, 还可以给每个网卡接口interface指定一个zone,
当网卡没有指定zone时,默认zone对该网卡生效
可以
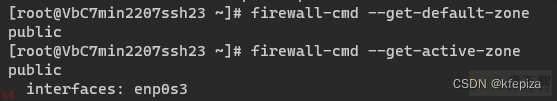
用firewall-cmd --get-default-zone查看默认zone ,
用firewall-offline-cmd --get-default-zone查看默认zone ,
用firewall-cmd --get-active-zone查看网卡接口zone
不能用firewall-offline-cmd --get-active-zone
 刚安装的Fedora 36 WorkStation版 的默认的zone和主网卡的zone 都是FedoraWorkstation
刚安装的Fedora 36 WorkStation版 的默认的zone和主网卡的zone 都是FedoraWorkstation ens33是vmware的默认主网卡名称, enp0s3是VirtualBox默认的主网卡名称
ens33是vmware的默认主网卡名称, enp0s3是VirtualBox默认的主网卡名称
查看当前活动zone只能用firewall-cmd开头 , 不能firewall-offline-cmd开头
sudo firewall-cmd --get-active-zone ### 查看当前活动zone
查看默认zone既可以用firewall-cmd开头 , 也能firewall-offline-cmd开头
sudo firewall-cmd --get-default-zone ### 查看默认zone
sudo firewall-offline-cmd --get-default-zone ### 查看默认zone
firewalld用xml文件保存zone模板,
可以到/usr/lib/firewalld/zones目录查看预定义的zone模板 或自定义的zone模板目录 /etc/firewalld/zones查看自定义的模板,自定义模板的目录一开始是空文件夹,如果对区域进行了修改,就会在自定义文件夹 /etc/firewalld/zones出现同名的xml,预定义文件夹/usr/lib/firewalld/zones的xml不会变化. 新增的自定义名称的zone也会出现在 /etc/firewalld/zones中cd /usr/lib/firewalld/zones ### 预定义的zone模板的目录
ls /usr/lib/firewalld/zones
cd /etc/firewalld/zones ### 自定义的zone模板的目录 , 该目录模板优先级高于预定义目录的模板
ls /usr/lib/firewalld/zones
cat /usr/lib/firewalld/zones/public.xml
cat /etc/firewalld/zones/public.xml ### 修改public才会出现
列出已定义的zone --get-zones , 包括预定义和自定义的zone , 只显示名称
sudo firewall-cmd --get-zones ### 列出所有区域的名称
sudo firewall-offline-cmd --get-zones ### 列出所有区域的名称
例如
CentOS 7 最小安装版sudo firewall-cmd --get-zones block dmz drop external home internal public trusted workCentOS 7 默认使用了firewalld预定义的zone中的publicFedora 36 WorkStation版
sudo firewall-cmd --get-zones FedoraServer FedoraWorkstation block dmz drop external home internal libvirt nm-shared public trusted workFedora 36 WorkStation版 默认并没有用firewalld预定义的zone , 而是自定义了一个新zone 名为 FedoraWorkstation
sudo firewall-cmd --list-all-zones ### 列出所有区域的配置详情
sudo firewall-offline-cmd --list-all-zones ### 列出所有区域的配置详情
sudo firewall-cmd --list-all ### 列出默认区域的配置详情
sudo firewall-offline-cmd --list-all ### 列出默认区域的配置详情
查看指定区域详情可以用--list-all --zone= 或者 --info-zone=
查看public区域的配置,添加的和启用的规则
sudo firewall-cmd --list-all --zone=public ### 查看public区域的配置详情
sudo firewall-offline-cmd --list-all --zone=public ### 查看public区域的配置详情
### 查看各预定义区域的配置,添加的和启用的规则
sudo firewall-cmd --zone=drop --list-all
sudo firewall-cmd --info-zone=drop
sudo firewall-offline-cmd --zone=drop --list-all
sudo firewall-offline-cmd --info-zone=drop
sudo firewall-cmd --zone=block --list-all
sudo firewall-cmd --info-zone=block
sudo firewall-offline-cmd --zone=block --list-all
sudo firewall-offline-cmd --info-zone=block
sudo firewall-cmd --zone=public --list-all
sudo firewall-cmd --info-zone=public
sudo firewall-offline-cmd --zone=public --list-all
sudo firewall-offline-cmd --info-zone=public
sudo firewall-cmd --zone=external --list-all
sudo firewall-cmd --info-zone=external
sudo firewall-offline-cmd --zone=external --list-all
sudo firewall-offline-cmd --info-zone=external
sudo firewall-cmd --zone=dmz --list-all
sudo firewall-cmd --info-zone=dmz
sudo firewall-offline-cmd --zone=dmz --list-all
sudo firewall-offline-cmd --info-zone=dmz
sudo firewall-cmd --zone=work --list-all
sudo firewall-cmd --info-zone=work
sudo firewall-offline-cmd --zone=work --list-all
sudo firewall-offline-cmd --info-zone=work
sudo firewall-cmd --zone=home --list-all
sudo firewall-cmd --info-zone=home
sudo firewall-offline-cmd --zone=home --list-all
sudo firewall-offline-cmd --info-zone=home
sudo firewall-cmd --zone=internal --list-all
sudo firewall-cmd --info-zone=internal
sudo firewall-offline-cmd --zone=internal --list-all
sudo firewall-offline-cmd --info-zone=internal
sudo firewall-cmd --zone=trusted --list-all
sudo firewall-cmd --info-zone=trusted
sudo firewall-offline-cmd --zone=trusted --list-all
sudo firewall-offline-cmd --info-zone=trusted
### 如果没有 --zone 参数, 就显示默认zone 的规则
sudo firewall-cmd --list-all ### 列出默认区域的配置详情
sudo firewall-offline-cmd --list-all ### 列出默认区域的配置详情
当一个网卡接口(例如lo)没有指定zone的时候, 就会使用默认zone的规则
可以用--remove-interface=选项来移除zone的interfaces对应的网卡, 使默认zone生效
sudo firewall-cmd --get-default-zone ### 查看默认zone是哪个区域
设置默认区域,带 --set-default-zone=的语句不用加--permanent就能永久生效, 也不能加--permanent
## 设置默认区域, 默认区域在没有区域时起作用
## 设置默认区域,带 ;--set-default-zone=;的语句不用加;--permanent;就能永久生效, 也不能加;--permanent;
### 设置默认区域为drop
sudo firewall-cmd --set-default-zone=drop
sudo firewall-offline-cmd --set-default-zone=drop
### 设置默认区域为block
sudo firewall-cmd --set-default-zone=block
sudo firewall-offline-cmd --set-default-zone=block
### 设置默认区域为public
sudo firewall-cmd --set-default-zone=public
sudo firewall-offline-cmd --set-default-zone=public
### 设置默认区域为external
sudo firewall-cmd --set-default-zone=external
sudo firewall-offline-cmd --set-default-zone=external
### 设置默认区域为dmz
sudo firewall-cmd --set-default-zone=dmz
sudo firewall-offline-cmd --set-default-zone=dmz
### 设置默认区域为work
sudo firewall-cmd --set-default-zone=work
sudo firewall-offline-cmd --set-default-zone=work
### 设置默认区域为home
sudo firewall-cmd --set-default-zone=home
sudo firewall-offline-cmd --set-default-zone=home
### 设置默认区域为internal
sudo firewall-cmd --set-default-zone=internal
sudo firewall-offline-cmd --set-default-zone=internal
### 设置默认区域为trusted
sudo firewall-cmd --set-default-zone=trusted
sudo firewall-offline-cmd --set-default-zone=trusted
### 查看默认区域的配置,添加的和启用的规则
sudo firewall-cmd --list-all
sudo firewall-offline-cmd --list-all
### 查看默认zone启用了哪些服务
sudo firewall-cmd --list-ports
sudo firewall-offline-cmd --list-ports
### 查看默认zone启用了哪些服务
sudo firewall-cmd --list-services
sudo firewall-offline-cmd --list-services
### 查看当前活动的zone区域,以及对应的网卡
sudo firewall-cmd --get-active-zones
### 查看lo网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=lo
sudo firewall-offline-cmd --get-zone-of-interface=lo
### 查看ens33网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=ens33
sudo firewall-offline-cmd --get-zone-of-interface=ens33
### 查看enp0s3网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=enp0s3
sudo firewall-offline-cmd --get-zone-of-interface=enp0s3
sudo firewall-cmd --permanent --remove-interface=网卡接口名
### 移除ens33网卡接口的zone
sudo firewall-cmd --permanent --remove-interface=ens33
sudo firewall-offline-cmd --remove-interface=ens33
### 查看ens33网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=ens33
sudo firewall-offline-cmd --get-zone-of-interface=ens33
### 移除enp0s3网卡接口的zone
sudo firewall-cmd --permanent --remove-interface=enp0s3
sudo firewall-offline-cmd --remove-interface=enp0s3
### 查看enp0s3网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=enp0s3
sudo firewall-offline-cmd --get-zone-of-interface=enp0s3
添加网络接口用--add-interface= , 网络接口必须没有zone
有zone的话用修改 --change-interface=
### 先移除ens33网卡接口的zone
sudo firewall-cmd --permanent --remove-interface=ens33
### 给ens33网卡接口添加pulic区域 , 要没有zone才能添加 , 加 --permanent 选项才能长久生效
sudo firewall-cmd --permanent --zone=public --add-interface=ens33
sudo firewall-offline-cmd --zone=public --add-interface=ens33
修改网络接口用--change-interface=
网络接口必须有zone,才能修改, 没有zone的话,用添加--add-interface=
修改ens33网卡接口的zone为public
### 修改ens33网卡接口的zone为public , 加 --permanent 选项才能长久生效
sudo firewall-cmd --permanent --zone=public --change-interface=ens33
### 查看ens33网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=ens33
修改ens33网卡接口的zone为internal
### 修改ens33网卡接口的zone为internal , 加 --permanent 选项才能长久生效
sudo firewall-cmd --permanent --zone=internal --change-interface=ens33
### 查看ens33网卡接口的zone
sudo firewall-cmd --get-zone-of-interface=ens33
新增zone和删除zone的语法对比
新增zone : --new-zone=删除zone : --delete-zone=新增zone : firewall-cmd --permanent --new-zone=自定义新zone名删除zone : firewall-cmd --permanent --delete-zone=Zone名称创建新区域语法firewall-cmd --new-zone=自定义zone名称 --permanent
创建新区域后要firewall-cmd --reload重新加载,或重启服务才起效
### 创建自定义的新zone , 取名NewCustomZone001
sudo firewall-cmd --new-zone=NewCustomZone001 --permanent
### 创建新区域后要重新加载或重启服务才起效 , 重新加载firewalld, 不能在firewalld服务处于停止状态的时候执行
sudo firewall-cmd --reload
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 创建自定义的新zone , 取名NewCustomZone001
sudo firewall-cmd --new-zone=NewCustomZone001 --permanent
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 列出所有区域的配置
sudo firewall-cmd --list-all-zones
### 创建新区域后要重新加载或重启服务才起效 , 重新加载firewalld, 不能在firewalld服务处于停止状态的时候执行
sudo firewall-cmd --reload
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 列出所有区域的配置
sudo firewall-cmd --list-all-zones
### 按名称删除zone
sudo firewall-cmd --permanent --delete-zone=Zone名称
创建删除zone测试
## 创建zone,删除zone 的测试
### 创建自定义的新zone , 取名NewCustomZone001
sudo firewall-cmd --new-zone=NewCustomZone001 --permanent
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 创建新区域后要重新加载或重启服务才起效 , 重新加载firewalld, 不能在firewalld服务处于停止状态的时候执行
sudo firewall-cmd --reload
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 按名称删除zone
sudo firewall-cmd --delete-zone=NewCustomZone001 --permanent
### 列出所有区域的名称
sudo firewall-cmd --get-zones
### 删除区域后要重新加载或重启服务才起效 , 重新加载firewalld, 不能在firewalld服务处于停止状态的时候执行
sudo firewall-cmd --reload
### 列出所有区域的名称
sudo firewall-cmd --get-zones
firewalld可以
直接在zone中添加端口 --zone= --add-port=先给zone添加service服务 --zone= --add-service=,### 开发zone的端口
sudo firewall-cmd --permanent --zone=myzone --add-port=80/tcp
sudo firewall-cmd --permanent --zone=myzone --add-port=3306-3399/tcp
sudo firewall-offline-cmd --zone=myzone --add-port=80/tcp
sudo firewall-offline-cmd --zone=myzone --add-port=3306-3399/tcp
### 开发service的端口
sudo firewall-cmd --permanent --service=myservice --add-port=80/tcp
sudo firewall-cmd --permanent --service=myservice --add-port=3306-3399/tcp
sudo firewall-offline-cmd --service=myservice --add-port=80/tcp
sudo firewall-offline-cmd --service=myservice --add-port=3306-3399/tcp
sudo firewall-cmd --list-ports ### 列出 默认zone 开放的端口
sudo firewall-cmd --list-ports --zone=public ### 列出 名为public的zone 开放的端口
sudo firewall-offline-cmd --list-ports ### 列出 默认zone 开放的端口
sudo firewall-offline-cmd --list-ports --zone=public ### 列出 名为public的zone 开放的端口
sudo firewall-offline-cmd --list-ports --service=mysql ### 列出 名为mysql的service 开放的端口
注意,即便没有22端口,也不代表22端口没有放行
发现firewalld默认的public区没有开启任何端口,但是却允许ssh,
原因是public区开启了ssh服务
ssh配置模板文件之/usr/lib/firewalld/services/ssh.xml ;
[root;Vmw-C7-2207-min z]# cat /usr/lib/firewalld/services/ssh.xml
<?xml version=;1.0; encoding=;utf-8;?>
<service>
<short>SSH</short>
<description>Secure Shell (SSH) is a protocol for logging into and executing commands on remote machines. It provides secure encrypted communications. If you plan on accessing your machine remotely via SSH over a firewalled interface, enable this option. You need the openssh-server package installed for this option to be useful.</description>
<port protocol=;tcp; port=;22;/>
</service>
firewalld官方文档—开启端口或服务—Open a Port or Service
加上--permanent则永久生效, 不加则重启失效加上--zone= 则在指定的区域生效 , 不加则在默认区域default-zone生效 , 等号可以换成空格加上 --service= 则在指定的服务生效### 开放public区域的80端口, 永久生效
sudo firewall-cmd --zone=public --add-port=80/tcp --permanent
### 关闭public区域的80端口, 永久生效
sudo firewall-cmd --zone=public --remove-port=80/tcp --permanent
### 开放public区域的80端口, 永久生效
sudo firewall-offline-cmd --zone=public --add-port=80/tcp
### 关闭public区域的80端口, 永久生效
sudo firewall-offline-cmd --zone=public --remove-port=80/tcp
sudo firewall-cmd --reload
如果不用--zone指定区域, 就是默认区域
sudo firewall-cmd --permanent --add-port=80/tcp
sudo firewall-cmd --permanent --add-port=88/udp
sudo firewall-cmd --permanent --add-port 443/tcp
sudo firewall-cmd --permanent --add-port 444/udp
sudo firewall-offline-cmd --add-port=80/tcp
sudo firewall-offline-cmd --add-port=88/udp
sudo firewall-offline-cmd --add-port 443/tcp
sudo firewall-offline-cmd --add-port 444/udp
sudo firewall-cmd --permanent --add-port=22/tcp
sudo firewall-cmd --permanent --add-port=80/tcp
sudo firewall-cmd --permanent --add-port=443/tcp
sudo firewall-cmd --permanent --add-port=1443/tcp
sudo firewall-cmd --permanent --add-port=3306/tcp
sudo firewall-cmd --permanent --add-port=22/tcp --zone=public
sudo firewall-cmd --permanent --add-port=80/tcp --zone=public
sudo firewall-cmd --permanent --add-port=443/tcp --zone=public
sudo firewall-cmd --permanent --add-port=1443/tcp --zone=public
sudo firewall-cmd --permanent --add-port=3306/tcp --zone=public
sudo firewall-offline-cmd --add-port=22/tcp
sudo firewall-offline-cmd --add-port=80/tcp
sudo firewall-offline-cmd --add-port=443/tcp
sudo firewall-offline-cmd --add-port=1443/tcp
sudo firewall-offline-cmd --add-port=3306/tcp
sudo firewall-offline-cmd --add-port=22/tcp --zone=public
sudo firewall-offline-cmd --add-port=80/tcp --zone=public
sudo firewall-offline-cmd --add-port=443/tcp --zone=public
sudo firewall-offline-cmd --add-port=1443/tcp --zone=public
sudo firewall-offline-cmd --add-port=3306/tcp --zone=public
firewalld本身是一项服务, firewalld下还有service服务方便端口配置, 此服务非彼服务
firewalld预定义了一些其它应用或服务的网络通行规则,称为service, 如ssh,http,https , 这些service服务规则以xml的格式保存,
预定义的服务.xml,默认文件夹是 /usr/lib/firewalld/services/
cd /usr/lib/firewalld/services/
ls /usr/lib/firewalld/services/
sudo cat -n /usr/lib/firewalld/services/ssh.xml
sudo cat -n /usr/lib/firewalld/services/FTP.xml
sudo cat -n /usr/lib/firewalld/services/http.xml
sudo cat -n /usr/lib/firewalld/services/https.xml
sudo cat -n /usr/lib/firewalld/services/mssql.xml
sudo cat -n /usr/lib/firewalld/services/mysql.xml
sudo cat -n /usr/lib/firewalld/services/git.xml
sudo cat -n /usr/lib/firewalld/services/svn.xml
下面的结果来自CentOS7 2207
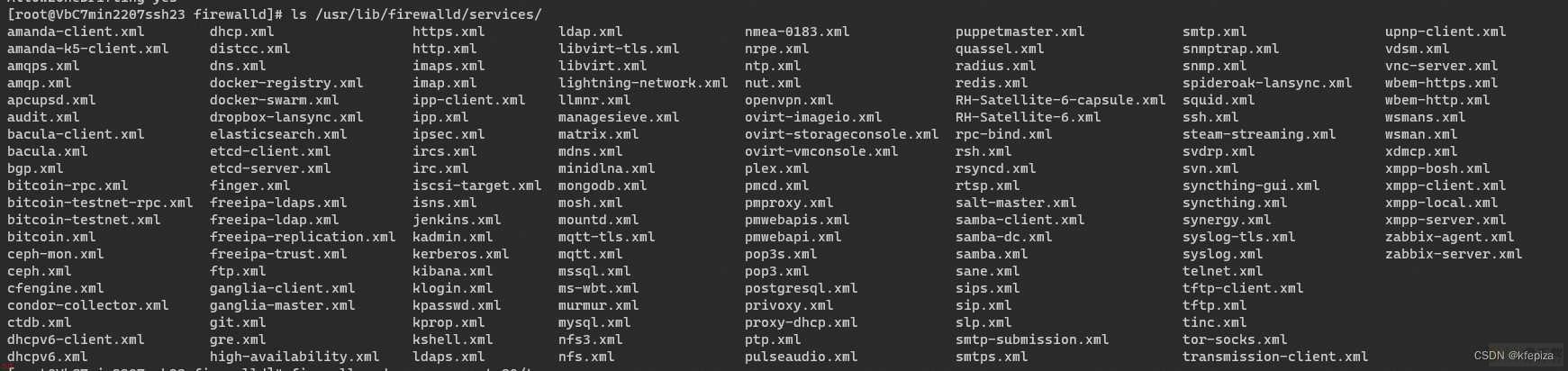
ls /usr/lib/firewalld/services/
amanda-client.xml dhcp.xml https.xml ldap.xml nmea-0183.xml puppetmaster.xml smtp.xml upnp-client.xml
amanda-k5-client.xml distcc.xml http.xml libvirt-tls.xml nrpe.xml quassel.xml snmptrap.xml vdsm.xml
amqps.xml DNS.xml imaps.xml libvirt.xml ntp.xml radius.xml snmp.xml vnc-server.xml
amqp.xml docker-registry.xml imap.xml lightning-network.xml nut.xml redis.xml spideroak-lansync.xml wbem-https.xml
apcupsd.xml docker-swarm.xml ipp-client.xml llmnr.xml openvpn.xml RH-Satellite-6-capsule.xml squid.xml wbem-http.xml
audit.xml dropbox-lansync.xml ipp.xml managesieve.xml ovirt-imageio.xml RH-Satellite-6.xml ssh.xml wsmans.xml
bacula-client.xml elasticsearch.xml ipsec.xml matrix.xml ovirt-storageconsole.xml rpc-bind.xml steam-streaming.xml wsman.xml
bacula.xml etcd-client.xml ircs.xml mdns.xml ovirt-vmconsole.xml rsh.xml svdrp.xml xdmcp.xml
bgp.xml etcd-server.xml irc.xml minidlna.xml plex.xml rsyncd.xml svn.xml xmpp-bosh.xml
bitcoin-rpc.xml finger.xml iscsi-target.xml mongodb.xml pmcd.xml rTSP.xml syncthing-gui.xml xmpp-client.xml
bitcoin-testnet-rpc.xml freeipa-ldaps.xml isns.xml mosh.xml pmproxy.xml salt-master.xml syncthing.xml xmpp-local.xml
bitcoin-testnet.xml freeipa-ldap.xml jenkins.xml mountd.xml pmwebapis.xml samba-client.xml synergy.xml xmpp-server.xml
bitcoin.xml freeipa-replication.xml kadmin.xml mqtt-tls.xml pmwebapi.xml samba-dc.xml syslog-tls.xml zabbix-agent.xml
ceph-mon.xml freeipa-trust.xml kerberos.xml mqtt.xml pop3s.xml samba.xml syslog.xml zabbix-server.xml
ceph.xml ftp.xml kibana.xml mssql.xml pop3.xml sane.xml telnet.xml
cfengine.xml ganglia-client.xml klogin.xml ms-wbt.xml PostgreSQL.xml sips.xml tftp-client.xml
condor-collector.xml ganglia-master.xml kpasswd.xml murmur.xml privoxy.xml sip.xml tftp.xml
ctdb.xml git.xml kprop.xml mysql.xml proxy-dhcp.xml slp.xml tinc.xml
dhcpv6-client.xml gre.xml kshell.xml nfs3.xml ptp.xml smtp-submission.xml tor-socks.xml
dhcpv6.xml high-availability.xml ldaps.xml nfs.xml pulseaudio.xml smtps.xml transmission-client.xml
自定义的service.xml在/etc/firewalld/services目录, 一开始为空文件夹
cd /etc/firewalld/services
ls /etc/firewalld/services
### 查看还有哪些服务可以打开
sudo firewall-cmd --get-services
### 查看还有哪些服务可以打开 老版本可用,新版本不行
sudo firewall-cmd --get-service
### 查看默认zone启用了哪些服务
sudo firewall-cmd --list-services
添加服务用 --add-service= 服务名 ,
加上 --permanent 才会永久生效 ,用--zone=区域名指定将服务添加到哪个区域, 如果不指定--zone=区域,则服务添加到默认的区域 default-zone 指向的区域sudo firewall-cmd --permanent --zone=dmz --add-service=http
sudo firewall-cmd --permanent --zone=dmz --add-service=https
sudo firewall-cmd --permanent --add-service=ssh
sudo firewall-cmd --permanent --add-service=http
sudo firewall-cmd --permanent --add-service=https
sudo firewall-cmd --permanent --add-service=mssql
sudo firewall-cmd --permanent --add-service=mysql
firewalld官方文档 —添加一个自定义的服务—https://firewalld.org/documentation/howto/add-a-service.html
添加新的空的服务service
sudo firewall-cmd --permanent --new-service=myservice ### 创建一个新service
或
sudo firewall-offline-cmd --new-service=myservice ### 创建一个新service
用firewall-cmd 命令添加一个新的空的服务
sudo firewall-cmd --permanent --new-service=myservice ### 创建一个新service
此时, 在/etc/firewalld/services目录 , 就多出一个 myservice.xml 文件
用firewall-cmd 命令配置这个服务
firewall-cmd --permanent --service=myservice --set-description=description
firewall-cmd --permanent --service=myservice --set-short=description
firewall-cmd --permanent --service=myservice --add-port=portid[-portid]/protocol
firewall-cmd --permanent --service=myservice --add-protocol=protocol
firewall-cmd --permanent --service=myservice --add-source-port=portid[-portid]/protocol
firewall-cmd --permanent --service=myservice --add-module=module
firewall-cmd --permanent --service=myservice --set-destination=ipv:address[/mask]
firewall-cmd --permanent --service=myservice --set-description=这个服务的描述
firewall-cmd --permanent --service=myservice --set-short=这个服务的简短描述
firewall-cmd --permanent --service=myservice --add-port=1025-65535/udp ### 连续端口
firewall-cmd --permanent --service=myservice --add-port=30000-65535/tcp ### 连续端口
firewall-cmd --permanent --service=myservice --add-port=22/tcp ### 单个端口
firewall-cmd --permanent --service=myservice --add-port=80/tcp
firewall-cmd --permanent --service=myservice --add-port=443/tcp
firewall-cmd --permanent --service=myservice --add-port=1433-1499/tcp
firewall-cmd --permanent --service=myservice --add-port=3306-3399/tcp
firewall-cmd --permanent --service=myservice --add-protocol=protocol
firewall-cmd --permanent --service=myservice --add-source-port=portid[-portid]/protocol
firewall-cmd --permanent --service=myservice --add-module=module
firewall-cmd --permanent --service=myservice --set-destination=ipv4:192.168.168.168/24
firewall-cmd --permanent --service=myservice --set-destination=ipv6:192.168.168.168/24
用firewall-offline-cmd 命令添加一个新的空的服务
firewall-offline-cmd --new-service=myservice
用firewall-offline-cmd 命令配置这个服务
firewall-offline-cmd --service=myservice --set-description=description
firewall-offline-cmd --service=myservice --set-short=description
firewall-offline-cmd --service=myservice --add-port=portid[-portid]/protocol
firewall-offline-cmd --service=myservice --add-protocol=protocol
firewall-offline-cmd --service=myservice --add-source-port=portid[-portid]/protocol
firewall-offline-cmd --service=myservice --add-module=module
firewall-offline-cmd --service=myservice --set-destination=ipv:address[/mask]
sudo firewall-cmd --permanent --zone=public --add-service=mysql;
sudo firewall-cmd --permanent --service=mysql --add-port=3306-3399/tcp; ## 添加服务的端口
sudo firewall-cmd --permanent --service=mysql --remove-port=3306-3399/tcp; ## 删除服务的端口
来自帮助文档的说明
--delete-service=<service>
Delete an existing service [P only]
--remove-service=<service>
Remove a service from a zone [P] [Z]
systemctl status firewalld ### firewalld服务状态
firewall-cmd --state ### firewalld是否启动
firewall-cmd --version ### firewalld的版本
sudo firewall-offline-cmd --get-default-zone ### 查看默认zone是哪个区
sudo firewall-cmd --get-default-zone ### 查看默认zone是哪个区
sudo firewall-cmd --get-active-zone ### 查看当前活动的区域
sudo firewall-cmd --list-ports ### 查看默认zone的端口
sudo firewall-cmd --list-ports --zone=public ### 查看public zone的端口
sudo firewall-cmd --permanent --get-ports --service=mysql ### 查看mysql service的端口
sudo firewall-cmd --panic-on
sudo firewall-cmd --panic-off
sudo firewall-cmd --query-panic ### 查看是否开启了紧急模式
例子
sudo firewall-cmd --query-panic ### 查看是否开启了紧急模式
sudo firewall-cmd --panic-on ### 开启紧急模式
sudo firewall-cmd --query-panic ### 查看是否开启了紧急模式
sudo firewall-cmd --panic-off ### 关闭紧急模式
sudo firewall-cmd --query-panic ### 查看是否开启了紧急模式
[root;Vmw-C7-2207-min ~]# firewall-cmd --query-panic
firewall-cmd --query-panic
sudo firewall-cmd --panic-off
firewall-cmd --query-panic
no
[root;Vmw-C7-2207-min ~]# sudo firewall-cmd --panic-on
success
[root;Vmw-C7-2207-min ~]# firewall-cmd --query-panic
yes
[root;Vmw-C7-2207-min ~]# sudo firewall-cmd --panic-off
success
[root;Vmw-C7-2207-min ~]# firewall-cmd --query-panic
no
查错命令 firewalld --nofork --debug
sudo firewalld --nofork --debug
Firewalld官方文档—查错—Debug firewalld
firewall-cmd --help | grep port
--get-ipset-types Print the supported ipset types
--service=<service> --add-port=<portid>[-<portid>]/<protocol>
Add a new port to service [P only]
--service=<service> --remove-port=<portid>[-<portid>]/<protocol>
Remove a port from service [P only]
--service=<service> --query-port=<portid>[-<portid>]/<protocol>
Return whether the port has been added for service [P only]
--service=<service> --get-ports
List ports of service [P only]
--service=<service> --add-source-port=<portid>[-<portid>]/<protocol>
Add a new source port to service [P only]
--service=<service> --remove-source-port=<portid>[-<portid>]/<protocol>
Remove a source port from service [P only]
--service=<service> --query-source-port=<portid>[-<portid>]/<protocol>
Return whether the source port has been added for service [P only]
--service=<service> --get-source-ports
List source ports of service [P only]
--list-ports List ports added for a zone [P] [Z]
--add-port=<portid>[-<portid>]/<protocol>
Add the port for a zone [P] [Z] [T]
--remove-port=<portid>[-<portid>]/<protocol>
Remove the port from a zone [P] [Z]
--query-port=<portid>[-<portid>]/<protocol>
Return whether the port has been added for zone [P] [Z]
--list-source-ports List source ports added for a zone [P] [Z]
--add-source-port=<portid>[-<portid>]/<protocol>
Add the source port for a zone [P] [Z] [T]
--remove-source-port=<portid>[-<portid>]/<protocol>
Remove the source port from a zone [P] [Z]
--query-source-port=<portid>[-<portid>]/<protocol>
Return whether the source port has been added for zone [P] [Z]
--list-forward-ports List IPv4 forward ports added for a zone [P] [Z]
--add-forward-port=port=<portid>[-<portid>]:proto=<protocol>[:toport=<portid>[-<portid>]][:toaddr=<address>[/<mask>]]
Add the IPv4 forward port for a zone [P] [Z] [T]
--remove-forward-port=port=<portid>[-<portid>]:proto=<protocol>[:toport=<portid>[-<portid>]][:toaddr=<address>[/<mask>]]
Remove the IPv4 forward port from a zone [P] [Z]
--query-forward-port=port=<portid>[-<portid>]:proto=<protocol>[:toport=<portid>[-<portid>]][:toaddr=<address>[/<mask>]]
Return whether the IPv4 forward port has been added for
--helper=<helper> --add-port=<portid>[-<portid>]/<protocol>
Add a new port to helper [P only]
--helper=<helper> --remove-port=<portid>[-<portid>]/<protocol>
Remove a port from helper [P only]
--helper=<helper> --query-port=<portid>[-<portid>]/<protocol>
Return whether the port has been added for helper [P only]
--helper=<helper> --get-ports
List ports of helper [P only]
firewall-cmd --help | grep ;service;
--get-services Print predefined services [P]
--new-service=<service>
Add a new service [P only]
--new-service-from-file=<filename> [--name=<service>]
Add a new service from file with optional name [P only]
--delete-service=<service>
Delete an existing service [P only]
--load-service-defaults=<service>
--info-service=<service>
Print information about a service
--path-service=<service>
Print file path of a service [P only]
--service=<service> --set-description=<description>
Set new description to service [P only]
--service=<service> --get-description
Print description for service [P only]
--service=<service> --set-short=<description>
Set new short description to service [P only]
--service=<service> --get-short
Print short description for service [P only]
--service=<service> --add-port=<portid>[-<portid>]/<protocol>
Add a new port to service [P only]
--service=<service> --remove-port=<portid>[-<portid>]/<protocol>
Remove a port from service [P only]
--service=<service> --query-port=<portid>[-<portid>]/<protocol>
Return whether the port has been added for service [P only]
--service=<service> --get-ports
List ports of service [P only]
--service=<service> --add-protocol=<protocol>
Add a new protocol to service [P only]
--service=<service> --remove-protocol=<protocol>
Remove a protocol from service [P only]
--service=<service> --query-protocol=<protocol>
Return whether the protocol has been added for service [P only]
--service=<service> --get-protocols
List protocols of service [P only]
--service=<service> --add-source-port=<portid>[-<portid>]/<protocol>
Add a new source port to service [P only]
--service=<service> --remove-source-port=<portid>[-<portid>]/<protocol>
Remove a source port from service [P only]
--service=<service> --query-source-port=<portid>[-<portid>]/<protocol>
Return whether the source port has been added for service [P only]
--service=<service> --get-source-ports
List source ports of service [P only]
--service=<service> --add-module=<module>
Add a new module to service [P only]
--service=<service> --remove-module=<module>
Remove a module from service [P only]
--service=<service> --query-module=<module>
Return whether the module has been added for service [P only]
--service=<service> --get-modules
List modules of service [P only]
--service=<service> --set-destination=<ipv>:<address>[/<mask>]
Set destination for ipv to address in service [P only]
--service=<service> --remove-destination=<ipv>
Disable destination for ipv i service [P only]
--service=<service> --query-destination=<ipv>:<address>[/<mask>]
Return whether destination ipv is set for service [P only]
--service=<service> --get-destinations
List destinations in service [P only]
--list-services List services added for a zone [P] [Z]
--add-service=<service>
Add a service for a zone [P] [Z] [T]
--remove-service=<service>
Remove a service from a zone [P] [Z]
--query-service=<service>
Return whether service has been added for a zone [P] [Z]
firewall-cmd --help | grep zone
--get-default-zone Print default zone for connections and interfaces
--set-default-zone=<zone>
Set default zone
--get-active-zones Print currently active zones
--get-zones Print predefined zones [P]
--get-zone-of-interface=<interface>
Print name of the zone the interface is bound to [P]
--get-zone-of-source=<source>[/<mask>]|<MAC>|ipset:<ipset>
Print name of the zone the source is bound to [P]
--list-all-zones List everything added for or enabled in all zones [P]
--new-zone=<zone> Add a new zone [P only]
--new-zone-from-file=<filename> [--name=<zone>]
Add a new zone from file with optional name [P only]
--delete-zone=<zone> Delete an existing zone [P only]
--load-zone-defaults=<zone>
Load zone default settings [P only] [Z]
--zone=<zone> Use this zone to set or query options, else default zone
--get-target Get the zone target [P only] [Z]
Set the zone target [P only] [Z]
--info-zone=<zone> Print information about a zone
--path-zone=<zone> Print file path of a zone [P only]
--list-all List everything added for or enabled in a zone [P] [Z]
--list-services List services added for a zone [P] [Z]
Set new description to zone [P only] [Z]
--get-description Print description for zone [P only] [Z]
Set new short description to zone [P only] [Z]
--get-short Print short description for zone [P only] [Z]
Add a service for a zone [P] [Z] [T]
Remove a service from a zone [P] [Z]
Return whether service has been added for a zone [P] [Z]
--list-ports List ports added for a zone [P] [Z]
Add the port for a zone [P] [Z] [T]
Remove the port from a zone [P] [Z]
Return whether the port has been added for zone [P] [Z]
--list-protocols List protocols added for a zone [P] [Z]
Add the protocol for a zone [P] [Z] [T]
Remove the protocol from a zone [P] [Z]
Return whether the protocol has been added for zone [P] [Z]
--list-source-ports List source ports added for a zone [P] [Z]
Add the source port for a zone [P] [Z] [T]
Remove the source port from a zone [P] [Z]
Return whether the source port has been added for zone [P] [Z]
--list-icmp-blocks List Internet ICMP type blocks added for a zone [P] [Z]
Add an ICMP block for a zone [P] [Z] [T]
Remove the ICMP block from a zone [P] [Z]
Return whether an ICMP block has been added for a zone
Enable inversion of icmp blocks for a zone [P] [Z]
Disable inversion of icmp blocks for a zone [P] [Z]
for a zone [P] [Z]
--list-forward-ports List IPv4 forward ports added for a zone [P] [Z]
Add the IPv4 forward port for a zone [P] [Z] [T]
Remove the IPv4 forward port from a zone [P] [Z]
a zone [P] [Z]
--add-masquerade Enable IPv4 masquerade for a zone [P] [Z] [T]
--remove-masquerade Disable IPv4 masquerade for a zone [P] [Z]
zone [P] [Z]
--list-rich-rules List rich language rules added for a zone [P] [Z]
Add rich language rule ;rule; for a zone [P] [Z] [T]
Remove rich language rule ;rule; from a zone [P] [Z]
added for a zone [P] [Z]
--list-interfaces List interfaces that are bound to a zone [P] [Z]
Bind the <interface> to a zone [P] [Z]
Change zone the <interface> is bound to [P] [Z]
Query whether <interface> is bound to a zone [P] [Z]
Remove binding of <interface> from a zone [P] [Z]
--list-sources List sources that are bound to a zone [P] [Z]
Bind the source to a zone [P] [Z]
Change zone the source is bound to [Z]
Query whether the source is bound to a zone [P] [Z]
Remove binding of the source from a zone [P] [Z]
firewall-cmd --help | grep interface
--get-default-zone Print default zone for connections and interfaces
--get-zone-of-interface=<interface>
Print name of the zone the interface is bound to [P]
--list-interfaces List interfaces that are bound to a zone [P] [Z]
--add-interface=<interface>
Bind the <interface> to a zone [P] [Z]
--change-interface=<interface>
Change zone the <interface> is bound to [P] [Z]
--query-interface=<interface>
Query whether <interface> is bound to a zone [P] [Z]
--remove-interface=<interface>
Remove binding of <interface> from a zone [P] [Z]
firewall-cmd --help | grep ;--set;
--set-log-denied=<value>
--set-default-zone=<zone>
--ipset=<ipset> --set-description=<description>
--ipset=<ipset> --set-short=<description>
--icmptype=<icmptype> --set-description=<description>
--icmptype=<icmptype> --set-short=<description>
--service=<service> --set-description=<description>
--service=<service> --set-short=<description>
--service=<service> --set-destination=<ipv>:<address>[/<mask>]
--set-description=<description>
--set-target=<target>
--set-short=<description>
--set-priority=<priority>
--helper=<helper> --set-description=<description>
--helper=<helper> --set-short=<description>
--helper=<helper> --set-module=<module>
--helper=<helper> --set-family={ipv4|ipv6|}
firewall-cmd --help | grep ;--get;
--get-log-denied Print the log denied value
--get-automatic-helpers
--get-default-zone Print default zone for connections and interfaces
--get-active-zones Print currently active zones
--get-zones Print predefined zones [P]
--get-services Print predefined services [P]
--get-icmptypes Print predefined icmptypes [P]
--get-zone-of-interface=<interface>
--get-zone-of-source=<source>[/<mask>]|<MAC>|ipset:<ipset>
--get-target Get the zone target [P only] [Z]
--get-ipset-types Print the supported ipset types
--get-ipsets Print predefined ipsets
--ipset=<ipset> --get-description
--ipset=<ipset> --get-short
--ipset=<ipset> --get-entries
--icmptype=<icmptype> --get-description
--icmptype=<icmptype> --get-short
--icmptype=<icmptype> --get-destinations
--service=<service> --get-description
--service=<service> --get-short
--service=<service> --get-ports
--service=<service> --get-protocols
--service=<service> --get-source-ports
--service=<service> --get-modules
--service=<service> --get-destinations
--get-description Print description for zone [P only] [Z]
--get-short Print short description for zone [P only] [Z]
--get-helpers Print predefined helpers
--helper=<helper> --get-description
--helper=<helper> --get-short
--helper=<helper> --get-ports
--helper=<helper> --get-module
--helper=<helper> --get-family
--get-all-chains
--get-chains {ipv4|ipv6|eb} <table>
--get-all-rules
--get-rules {ipv4|ipv6|eb} <table> <chain>
--get-all-passthroughs
--get-passthroughs {ipv4|ipv6|eb} <arg>...
firewall-cmd --help | grep ;--list;
--list-all-zones List everything added for or enabled in all zones [P]
--list-all-policies List everything added for or enabled in all policies
--list-all List everything added for or enabled [P] [Z] [O]
--list-services List services added [P] [Z]
--list-ports List ports added [P] [Z] [O]
--list-protocols List protocols added [P] [Z] [O]
--list-source-ports List source ports added [P] [Z] [O]
--list-icmp-blocks List Internet ICMP type blocks added [P] [Z] [O]
--list-forward-ports List IPv4 forward ports added [P] [Z] [O]
--list-rich-rules List rich language rules added [P] [Z] [O]
--list-ingress-zones
--list-egress-zones
--list-interfaces List interfaces that are bound to a zone [P] [Z]
--list-sources List sources that are bound to a zone [P] [Z]
--list-lockdown-whitelist-commands
--list-lockdown-whitelist-contexts
--list-lockdown-whitelist-uids
--list-lockdown-whitelist-users
firewall-cmd --help | grep ;--new;
--new-zone=<zone> Add a new zone [P only]
--new-zone-from-file=<filename> [--name=<zone>]
--new-policy=<policy>
--new-policy-from-file=<filename> [--name=<policy>]
--new-ipset=<ipset> --type=<ipset type> [--option=<key>[=<value>]]..
--new-ipset-from-file=<filename> [--name=<ipset>]
--new-icmptype=<icmptype>
--new-icmptype-from-file=<filename> [--name=<icmptype>]
--new-service=<service>
--new-service-from-file=<filename> [--name=<service>]
--new-helper=<helper> --module=<module> [--family=<family>]
--new-helper-from-file=<filename> [--name=<helper>]
firewall-cmd --help | grep ;--add;
--ipset=<ipset> --add-entry=<entry>
--ipset=<ipset> --add-entries-from-file=<entry>
--icmptype=<icmptype> --add-destination=<ipv>
--service=<service> --add-port=<portid>[-<portid>]/<protocol>
--service=<service> --add-protocol=<protocol>
--service=<service> --add-source-port=<portid>[-<portid>]/<protocol>
--service=<service> --add-module=<module>
--add-service=<service>
--add-port=<portid>[-<portid>]/<protocol>
--add-protocol=<protocol>
--add-source-port=<portid>[-<portid>]/<protocol>
--add-icmp-block=<icmptype>
--add-icmp-block-inversion
--add-forward-port=port=<portid>[-<portid>]:proto=<protocol>[:toport=<portid>[-<portid>]][:toaddr=<address>[/<mask>]]
--add-masquerade Enable IPv4 masquerade for a zone [P] [Z] [T]
--add-rich-rule=<rule>
--add-interface=<interface>
--add-source=<source>[/<mask>]|<MAC>|ipset:<ipset>
--helper=<helper> --add-port=<portid>[-<portid>]/<protocol>
--add-chain {ipv4|ipv6|eb} <table> <chain>
--add-rule {ipv4|ipv6|eb} <table> <chain> <priority> <arg>...
--add-passthrough {ipv4|ipv6|eb} <arg>...
--add-lockdown-whitelist-command=<command>
--add-lockdown-whitelist-context=<context>
--add-lockdown-whitelist-uid=<uid>
--add-lockdown-whitelist-user=<user>
firewall-cmd --help | grep ;--change;
--change-interface=<interface>
--change-source=<source>[/<mask>]|<MAC>|ipset:<ipset>
firewall-cmd --help | grep ;--delete;
--delete-zone=<zone> Delete an existing zone [P only]
--delete-ipset=<ipset>
--delete-icmptype=<icmptype>
--delete-service=<service>
--delete-helper=<helper>
firewall-cmd --help | grep ;--remove;
--ipset=<ipset> --remove-entry=<entry>
--ipset=<ipset> --remove-entries-from-file=<entry>
--icmptype=<icmptype> --remove-destination=<ipv>
--service=<service> --remove-port=<portid>[-<portid>]/<protocol>
--service=<service> --remove-protocol=<protocol>
--service=<service> --remove-source-port=<portid>[-<portid>]/<protocol>
--service=<service> --remove-helper=<helper>
--service=<service> --remove-destination=<ipv>
--service=<service> --remove-include=<service>
--remove-service=<service>
--remove-port=<portid>[-<portid>]/<protocol>
--remove-protocol=<protocol>
--remove-source-port=<portid>[-<portid>]/<protocol>
--remove-icmp-block=<icmptype>
--remove-forward-port=port=<portid>[-<portid>]:proto=<protocol>[:toport=<portid>[-<portid>]][:toaddr=<address>[/<mask>]]
--remove-masquerade Disable IPv4 masquerade [P] [Z] [O]
--remove-rich-rule=<rule>
--remove-icmp-block-inversion
--remove-forward Disable forwarding of packets between interfaces and
--remove-ingress-zone=<zone>
--remove-egress-zone=<zone>
--remove-interface=<interface>
--remove-source=<source>[/<mask>]|<MAC>|ipset:<ipset>
--helper=<helper> --remove-port=<portid>[-<portid>]/<protocol>
--remove-chain {ipv4|ipv6|eb} <table> <chain>
--remove-rule {ipv4|ipv6|eb} <table> <chain> <priority> <arg>...
--remove-rules {ipv4|ipv6|eb} <table> <chain>
--remove-passthrough {ipv4|ipv6|eb} <arg>...
--remove-lockdown-whitelist-command=<command>
--remove-lockdown-whitelist-context=<context>
--remove-lockdown-whitelist-uid=<uid>
--remove-lockdown-whitelist-user=<user>
--info相关的
firewall-cmd --help | grep ;--info;
--info-zone=<zone> Print information about a zone
--info-policy=<policy>
--info-ipset=<ipset> Print information about an ipset
--info-icmptype=<icmptype>
--info-service=<service>
--info-helper=<helper> Print information about an helper